On May 16, 2023, WordPress.org released a minor but essential security update, WordPress 6.2.1. This update, which follows the significant WordPress 6.2 release, addresses five security vulnerabilities impacting multiple WordPress core versions. This update is a significant step forward in enhancing the security and functionality of WordPress websites. This blog post will delve into the features, fixes, and impacts of the WordPress 6.2.1 security update.
Features of WordPress 6.2.1

The WordPress 6.2.1 release brought several enhancements and improvements to the platform. Some of the key features include:
20 Core Bug Fixes
The WordPress core team has diligently addressed issues affecting the functionality and security of millions of websites worldwide. In the 6.2.1 update, they fixed 20 core bugs that were causing various problems for users and developers alike. These fixes enhance WordPress’s overall performance and stability, making it a more reliable platform for everyone.
10 Block Editor Bug Fixes
In addition to the core bug fixes, the 6.2.1 update also includes 10 fixes specifically for the block editor. The block editor, or Gutenberg as it’s commonly known, is a relatively new feature in WordPress that has revolutionized the way users create content. These fixes ensure a smoother, more efficient content creation process.
Security Fixes in WordPress 6.2.1

The WordPress 6.2.1 update is not just about bug fixes; it’s also a security release. The WordPress security team has addressed five significant vulnerabilities in this update:
Block Themes Parsing Shortcodes in User-Generated Data:
This vulnerability allowed unauthenticated attackers to execute shortcodes in user-generated content, such as comments. This could potentially allow them to exploit vulnerabilities that typically require subscriber or contributor-level permissions.
Cross-Site Request Forgery (CSRF) Issue Updating Attachment Thumbnails:
The vulnerable code was located in the wp_ajax_set_attachment_thumbnail function. The function had a permission check using current_user_can, but it lacked a nonce check, resulting in a CSRF issue.
This flaw allowed unauthenticated users to update the thumbnail image associated with existing attachments if they could trick an authenticated user with appropriate permissions into performing an action, such as clicking a link. The patch for this issue involved implementing a nonce check.
A Flaw Allowing XSS (Cross Site Scripting) via Open Embed Auto Discovery:
This vulnerability allowed authenticated attackers with contributor-level or higher permissions to inject arbitrary web scripts in pages using a crafted oEmbed payload at a remote URL.
Bypassing of KSES Sanitization in Block Attributes for Low Privileged Users:
This vulnerability, discovered by a third-party security audit, allows authenticated attackers with contributor-level or higher permissions to embed arbitrary content in HTML comments on a page. Cross-Site Scripting attacks may be possible if combined with another vulnerability. This issue only affects sites using a block editor compatible theme.
A Path Traversal Issue via Translation Files:
This vulnerability, identified as CVE-2023-2745, was located in the determine_locale function, which acted as a handler to determine the current locale desired for the request. The function only used the sanitize_text_field function to sanitize the value, which was not sufficient enough to protect against directory traversal attacks.
This vulnerability allows unauthenticated attackers to access and load arbitrary translation files through the wp_lang parameter. Although challenging to exploit in most configurations, it could potentially be used to perform a Cross-Site Scripting attack if an attacker manages to upload a crafted translation file onto your site.
Impact of WordPress 6.2.1 Update
Impact on Websites
The WordPress 6.2.1 update has a significant impact on websites. It enhances security, improves performance, and fixes bugs that are causing issues for users. However, it’s important to note that the update also removed a key functionality that caused numerous plugins to stop working on sites that use the WordPress blocks system. This has caused some disruption, but the WordPress core team has been quick to address these issues.
Impact on Plugins
Several plugins were affected by the 6.2.1 update, ranging from forms to sliders to breadcrumbs. The removal of shortcode support from block templates caused some sites to become non-functional. However, WordPress released a rapid response release (6.2.2) to address this issue and further patch the vulnerability addressed in 6.2.1.
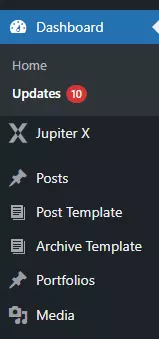
How to Update to WordPress 6.2.1

Updating to WordPress 6.2.1 is straightforward, especially if you have automatic background updates enabled. If not, you can manually update by following these steps:
- Backup your website – Always create a backup before updating to prevent data loss in case of issues.
- Go to your WordPress Dashboard.
- Click on “Updates”.

- Click on “Update Now”.
Remember to test your website thoroughly after the update to ensure everything is working as expected.

Conclusion
The WordPress 6.2.1 security and maintenance release is a crucial update that addresses several vulnerabilities and bugs. It enhances the security and performance of WordPress, making it a safer and more reliable platform for users and developers alike.
However, it’s important to note that the update has caused some disruption, particularly for sites that use the WordPress blocks system. The WordPress core team has been quick to address these issues, and a rapid response release (6.2.2) has already been issued to patch further the vulnerability addressed in 6.2.1 and restore shortcode functionality.
As always, it’s recommended to keep your WordPress site updated to the latest version to benefit from the latest features, security fixes, and bug fixes. If your site hasn’t been updated automatically, you can manually update it from your WordPress dashboard.
Remember, a secure website is not just beneficial for you as a site owner, but it also builds trust with your visitors, enhancing their user experience and your site’s reputation. So, make sure to stay updated and safe, and continue enjoying all the great features that WordPress has to offer.


WordPress 6.2.1 Security Release: Features, Impact, and Update Guide