Malware attacks are becoming increasingly sophisticated and pervasive, posing a serious threat to organizations and individuals alike. In 2022, ransomware attacks hit a record high, with the United States accounting for the largest share of global incidents. Businesses across all industries are at risk, as evidenced by the recent MCNA Dental data breach, which exposed the sensitive data of millions of customers.
While the threat landscape continues to evolve with new forms of malware emerging regularly, so too do the techniques for remediation. However, the malware remediation process can be complex and time-consuming, depending on the severity of the infection. Therefore, it is essential to remediate malware infections as quickly as possible to minimize the damage and protect your data.
This article will provide a comprehensive guide to malware remediation, covering the following topics:
- How to identify malware infections
- Different types of malware remediation techniques
- Best practices for malware remediation
- Emerging trends in malware remediation
By the end of this article, you will have a deep understanding of malware remediation and be able to protect your systems and networks from malware attacks effectively.
What is Malware Remediation?
Malware remediation refers to the systematic process of identifying, cleaning up, and recovering from malware attacks. It involves detecting the presence of malicious software, understanding its behavior, and taking appropriate measures to remove it from the system. The goal of malware remediation is not just to eliminate the immediate threat but also to ensure that the system is fortified against future attacks.
The Different Types of Malware Attacks
Malware, short for malicious software, encompasses a broad range of software programs designed to harm, exploit, steal sensitive data, or otherwise compromise the integrity, confidentiality, or availability of computer systems. Here are some of the most common types of malware attacks:
- Viruses: Malicious code that attaches itself to legitimate software and spreads to other programs and files on the same system or network.
- Worms: Standalone malware that replicates itself to spread across networks without user intervention.
- Trojan Horses: Disguised as legitimate software, Trojans create backdoors in security systems to allow other malware to enter.
- Ransomware Attack: Encrypts the victim’s data and demands a ransom for its decryption.
- Spyware: Covertly collects information about a user’s activities and sends it to a third party.
- Adware: Displays unwanted advertisements, often bundled with free software.
- Rootkits: Provides unauthorized access to a computer or network by exploiting system vulnerabilities.
- Fileless Malware: Operates in a system’s memory rather than on the hard drive, making it harder to detect.
- Botnets: Networks of compromised computers controlled by cybercriminals to launch coordinated attacks.
- Keyloggers: Records a user’s keystrokes to capture sensitive information like passwords.
- Mobile Malware: Specifically targets mobile devices, stealing data or causing disruptions.
- Exploit Kits: Automated tools that exploit known vulnerabilities in software to deliver malware.
Evolution of malware threats over the years
The first known malware was the Creeper worm, which infected ARPANET computers in 1971. It displayed the message, “I’m the creeper, catch me if you can!”.
In the 1980s and 1990s, malware spread mainly through floppy disks and email attachments. Some of the most notorious examples were Brain (the first PC virus), Jerusalem (a DOS virus that deleted files), Morris (a worm that caused a major internet slowdown), and Melissa (a macro virus that emailed itself to contacts).
In the 2000s and 2010s, malware became more sophisticated and diverse, exploiting web browsers, operating systems, applications, and network vulnerabilities. Some of the most impactful examples were ILOVEYOU (a worm that infected millions of computers), Stuxnet (a worm that sabotaged Iran’s nuclear program), CryptoLocker (a ransomware that encrypted files and demanded payment), and WannaCry (a ransomware that affected hundreds of thousands of computers worldwide).
In the 2020s and beyond, malware is expected to evolve further, using artificial intelligence, machine learning, social engineering, and stealth techniques to evade detection and cause damage. Some of the emerging threats include file-less malware (which resides in memory or system files), mobile malware (which targets smartphones and tablets), and crypto-jacking (which uses victims’ devices to mine cryptocurrency).
Why Traditional Malware Protection Isn’t Enough
Traditional malware protection relies on signature-based detection, which means it can only identify known threats based on their unique characteristics or “malware signatures.” However, this approach has several limitations:
- It cannot detect new or unknown threats, such as zero-day exploits and polymorphic malware, which change their appearance or behavior to avoid recognition.
- It requires frequent updates to keep up with the growing number and variety of malware variants. However, updates can be delayed or missed due to network issues or human errors.
- It consumes a lot of system resources and slows down performance, especially when scanning large or complex files.
What are the Challenges of Malware Remediation
The malware remediation process became increasingly challenging due to the sophistication of modern malware strains, their persistence mechanisms, hidden components, and the potential for significant business disruption during the remediation process.
The Complexity of Modern Malware Strains and Their Persistence Mechanisms
Modern malware strains are becoming increasingly complex and sophisticated. They often include Remote Access Trojans (RATs), banking Trojans, information stealers, and ransomware. These malware strains have been in use for more than five years, with their code bases evolving into multiple variations. This evolution makes it difficult for traditional antivirus solutions to detect and remove them effectively.
Moreover, these malware strains employ various persistence mechanisms to maintain their presence on an infected system. They often modify registry keys or use fileless techniques to achieve persistence. These techniques allow the malware to survive system reboots and continue operating even after initial detection and removal attempts.
Some common persistence mechanisms include:
- Registry keys: Malware can create or modify registry keys to ensure that it is executed at startup or when certain events occur.
- Scheduled tasks: Malware can create scheduled tasks to ensure that it is executed at regular intervals.
- Rootkits: Rootkits are a type of malware that can modify the operating system kernel, making them very difficult to detect and remove.
Hidden Malware Components
Hidden components of malware pose another significant challenge in the remediation process. Malware authors often use evasion techniques to make their malicious software appear “new” or “different” to evade security controls. These techniques include packing or crypting the original executable to change its binary fingerprint, making it difficult for antivirus software to detect the malware.
Some common hidden malware components include:
- Steganography: Steganography is the technique of hiding data within other data. Malware developers can use steganography to hide malware code within images, videos, or other files.
- Polymorphism: Polymorphism is the ability of malware to change its form or signature over time. This makes it difficult for security software to detect and remove polymorphic malware.
- Zero-day attacks: Zero-day attacks are attacks that exploit vulnerabilities in software that are not yet known to the software vendor. Malware developers can use zero-day attacks to infect systems with malware that is not detectable by security software.
Fileless malware is another example of a hidden component that poses a significant challenge. This type of malware doesn’t install anything initially but makes changes to files that are native to the operating system, such as PowerShell or WMI. Because these files are recognized as legitimate by the operating system, fileless attacks often go undetected by antivirus software.
Risk of Business Disruption During the Remediation Process
The process of malware remediation can cause significant business disruption. During remediation, critical systems may need to be taken offline, resulting in downtime that can impact productivity and revenue. Furthermore, if the remediation process is not handled correctly, there’s a risk of ransomware reinfection, leading to further business disruption.
In addition to these challenges, organizations also face other issues, such as resource constraints, lack of security maturity, and the constant emergence of new malware variants. Therefore, businesses must have a robust cybersecurity strategy in place that includes proactive measures such as regular system updates, employee training, and the use of advanced threat detection and response tools.
Malware Remediation Process
1. Preparation
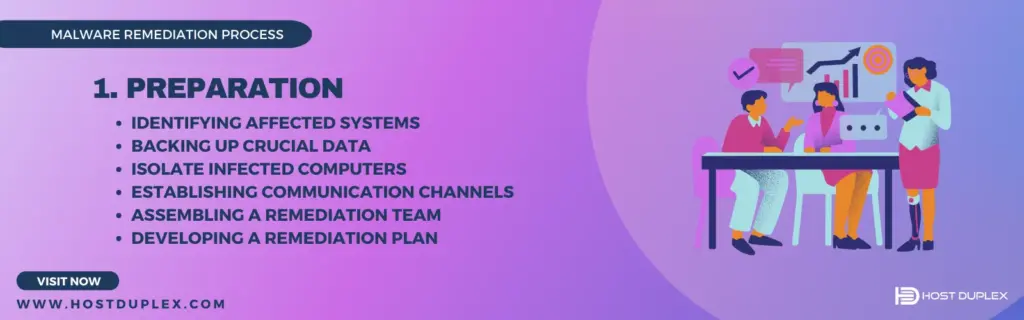
The first and foremost step in the malware remediation process is Preparation. This phase is crucial as it sets the groundwork for the subsequent steps in the remediation process. It involves several key activities:
- Identifying Affected Systems: The initial task is to identify and document all systems that have been affected by the malware. This could include servers, workstations, laptops, and other network devices. Identifying the scope of the infection helps in understanding the extent of the problem and planning the remediation strategy accordingly.
- Backing Up Crucial Data: Before starting the remediation process, it’s essential to back up all critical data. This ensures that valuable information is not lost during the remediation process. The backup should be stored in a secure location, separate from the network, to prevent it from being infected.
- Isolate Infected Computers: Infected systems can spread malware to other systems or command and control servers. To prevent this, infected devices should be isolated from the network. This could involve disconnecting them physically or logically (through network controls). Isolation helps contain the malware and prevents further damage.
- Establishing Communication Channels: Establishing secure communication channels ensures that all stakeholders are kept informed about the progress of the remediation process.
- Assembling a Remediation Team: Depending on the size and complexity of the incident, a dedicated team may be required to handle the remediation process. This team should include individuals with expertise in various areas, such as system administration, network security, and malware analysis.
- Developing a Remediation Plan: Based on the information gathered, a detailed remediation plan should be developed. This plan should outline the steps to be taken during the Detection, Removal, Verification, and Prevention phases of the remediation process.
2. Detection

The second phase in the malware remediation process is Detection. This stage involves identifying the presence of malware in a system using various techniques and tools. Here are some of the latest methods used for malware detection:
- Signature-Based Detection: This traditional method uses known digital indicators of malware, often maintained in a database, to identify suspicious behavior. However, it is reactive in nature and may not be effective against new, unknown malware.
- Behavior-Based Detection: This technique monitors the behavior of applications and processes to identify any abnormal or suspicious activities that could indicate a malware infection.
- Heuristic Detection: Heuristic detection uses algorithms to analyze the characteristics and behavior of files and programs to detect unknown or zero-day malware.
- Machine Learning Detection: Machine learning algorithms can be trained to recognize patterns and anomalies that indicate malware. This method can be particularly effective at detecting new and evolving threats.
- Automated Detection: Automated tools can continuously monitor systems for signs of malware, reducing the need for manual intervention.
- Sandboxing: Dynamic malware analysis executes suspected malicious code in a safe environment called a sandbox. This allows security professionals to observe and study the malware’s behavior without risking an actual system infection.
- Endpoint Detection: Endpoint detection and response (EDR), monitors and collects data from endpoints (such as computers or mobile devices) to detect and respond to threats. This can help provide visibility into the attack chain, identify root causes, contain incidents, and prevent recurrence.
Several malware detection tools are available that utilize these techniques. Remember, no single method or tool can guarantee complete protection against all types of malware. Therefore, using a combination of different techniques and tools can enhance the effectiveness of your malware detection efforts.
3. Reporting Malware and Associated Vulnerabilities to Regulators

In the event of a malware incident, it’s crucial to report the occurrence and any associated vulnerabilities to the appropriate regulatory bodies. This not only aids in the containment and mitigation of the current incident but also helps prevent similar incidents in the future. Here’s how you can go about it:
- Identify the Appropriate Regulatory Body: Depending on your geographical location and the nature of your business, different regulatory bodies may be responsible for handling reports of malware incidents. For instance, the Cybersecurity and Infrastructure Security Agency (CISA) is a key regulatory body in the United States.
- Prepare Your Report: Your report should include detailed information about the incident, such as how the malware was detected, what systems were affected, what data might have been compromised, and what steps have been taken so far.
- Submit Your Report: CISA provides secure means for constituents and partners to report incidents, phishing attempts, malware, and vulnerabilities. You can submit your report via their Incident Reporting Form.
- Follow-Up: After your report has been submitted, be sure to follow up for updates or additional instructions. The regulatory body may provide guidance on further steps to take or resources that can assist in your remediation efforts.
4. Removal
The third phase in the malware remediation process is Removal. This stage involves eliminating the identified malware from the infected systems. Here are some of the latest methods used for malware removal:
- Antivirus Software: Antivirus software is a powerful tool that can find and remove malware from your system. It’s important to keep your antivirus software up-to-date with the latest virus definitions to ensure it can effectively combat new threats.
- Manual Removal: In some cases, manual malware removal may be necessary. This could involve deleting temporary files, resetting browser settings, and removing malicious files and folders from your system.
- Safe Mode: Booting your system in Safe Mode can help in the removal process as it only loads the essential drivers and services. This prevents the malware from launching at startup, making removing it easier.
- System Restore: If the malware has significantly changed your system, you might need to perform a system restore. This will revert your system back to a previous state before the malware infection.
- Reformatting and Reinstalling: In extreme cases where the malware has deeply embedded itself into the system, reformatting the hard drive and reinstalling the operating system might be the only viable option.
- Advanced Malware Protection Solutions: Advanced malware protection solutions use techniques like whitelisting or allowlisting (which allows approved entities) and blocklisting (a list of entities that should be blocked). These solutions also use machine learning, heuristic scanning, and a massive malware database to detect and remove even the most sophisticated malware.
Remember, removing malware is just one part of the remediation process. After removal, it’s important to verify that the malware has been completely eliminated and take steps to prevent future infections.
5. Verification
The verification phase of the malware remediation process is a critical step that ensures the effectiveness of the previous stages and the overall integrity of the system post-remediation. This phase involves a series of actions aimed at confirming that the malware has been completely eradicated and that the system is secure.
Conducting Follow-Up Scans
After the removal process, it’s essential to conduct follow-up scans. These scans are performed using updated antivirus or anti-malware software to ensure no remnants of the malware are left in the system. The scans should be thorough, covering all files, folders, and sectors of the system. Any suspicious or flagged items should be investigated and dealt with accordingly.
Restoring Data from Backups
Data restoration from backups is another crucial aspect of verification. After a malware attack, some data may have been corrupted or deleted. Restoring from a clean, recent backup can help recover lost information and ensure business continuity. However, it’s important to verify that the backups themselves are free from malware to prevent re-infection.
System Integrity Checks
System integrity checks involve examining system files and settings to ensure they have not been altered by the malware. This includes checking registry entries, system files, and configurations. Any changes detected should be investigated and corrected as necessary.
6. Prevention
Prevention is the final yet arguably the most crucial step in the malware remediation process. It involves implementing strategies and practices to minimize the risk of future malware attacks. Here are some best practices to prevent malware:
Exercise Caution with Emails and Downloads
Approximately 90% of cyber attacks begin with a phishing email, text, or malicious link. Therefore, it’s essential to scrutinize emails for signs like misspellings, generic greetings, and suspicious attachments or links. Similarly, downloads are one of the surest ways to introduce malware into your system. Download software only from reputable sources and official websites.
Use Antivirus Software and Enable Firewall Protection
Utilize updated antivirus or anti-malware software to scan your system for potential threats regularly. Additionally, next-generation firewalls, network intrusion prevention systems (IPS), and virtual private networks can add an extra layer of security.
Keep Software Updated
Regularly updating your software is crucial, as updates often include patches for security vulnerabilities that could be exploited by malware.
Implement Multi-factor Authentication (MFA)
Implementing multi-factor authentication can add an extra layer of security by requiring users to provide two or more verification factors to gain access to a resource.
Regularly Back Up Your Data
Regular data backups can help recover lost information in case of a malware attack. However, ensure that the backups themselves are free from malware to prevent re-infection.
Educate Your Employees
Training your employees about the signs of a malware infection and how to respond appropriately can help prevent future infections and improve response times when an incident occurs.
Best Practices for Malware Remediation
Here are some best practices that can help enhance the effectiveness of your malware remediation efforts:
Regular Security Audits
Conducting regular security audits is a proactive measure that can help identify potential vulnerabilities before they can be exploited. These audits should include a thorough examination of all systems, networks, and applications to identify any areas that may be susceptible to malware attacks.
Reporting Suspected Malware and Related Vulnerabilities
Encourage users to report any suspected malware or related vulnerabilities. This can help in the early detection and containment of malware threats.
Limit Physical Access
Restricting physical access to computers to a few authorized users can greatly reduce the chances of system compromise by preventing malware transmission through emails, file downloads, and other compromising activities.
Disable Unnecessary Processes
Disabling unnecessary processes can reduce the potential attack surface for malware. This includes disabling unnecessary services, closing unused ports, and uninstalling unused software.
Secure Mobile Devices
With the increasing use of mobile devices in the workplace, it’s important to ensure these devices are also secure. This includes installing security software, regularly updating the operating system and apps, and implementing strong access controls.
Regularly Monitor Accounts
Regularly monitoring user accounts can help detect any unusual activity that may indicate a malware infection. This includes monitoring for multiple failed login attempts, unusual data transfers, or changes in user privileges.
Work with a Managed Security Services Provider (MSSP)
Working with a managed security services provider (MSSP) can provide additional expertise and resources for your malware remediation efforts. They can help define and implement malware remediation processes or manage the aftermath of a data breach.
Stay Informed About the Latest Threats
Staying updated on the latest threats is crucial for effective malware prevention. This involves gaining cybersecurity knowledge through continuous learning and staying informed about the latest malware threats.
Emerging Trends in Malware Remediation
Emerging trends in malware remediation are increasingly leveraging advanced technologies such as Artificial Intelligence (AI), Machine Learning (ML), and cloud-based solutions. Here’s a brief overview of each:
Artificial Intelligence (AI)
Artificial Intelligence (AI) is revolutionizing the field of malware remediation. AI supports the establishment of covert channels, as well as the obfuscation of malware. Additionally, AI results in new forms of phishing attacks and enables hard-to-detect cyber-physical sabotage. Malware creators increasingly deploy AI and Machine Learning (ML) methods to improve their attack capabilities. AI’s potential for automation of complex tasks serves as a challenge in the face of defensive deployment of anti-malware AI techniques.
For instance, AI can analyze large volumes of data and identify patterns and anomalies, enabling real-time detection and prevention of malware attacks. This is particularly useful in identifying zero-day threats that traditional signature-based detection methods might miss.
Machine Learning (ML)
Machine Learning (ML) is another powerful tool in the fight against malware. ML algorithms can learn from previous instances of malware attacks and improve their detection and removal capabilities over time. They have been used to automate static and dynamic analysis investigation where malware having similar behavior are clustered together, and based on the proximity, unknown malware get classified into their respective families.
For example, ML can analyze system calls, operational codes, sections, and byte codes from malware files. In one study, it was found that the feature vector for system calls yields the highest accuracy. This shows how ML can enhance the precision of malware detection.
Cloud-Based Remediation
Cloud-based solutions are gaining popularity due to their numerous benefits. Migrating on-premises resources to the cloud can provide many benefits for organizations, including a faster path to innovation, simpler access to applications and resources, and cost reductions.
Cloud-based malware detection detects and removes malware from cloud-based applications and ensures that applications remain malware-free. Once activated, all files in cloud-based services will be hashed and sent for malware scanning automatically. If the file contains malware, it can either be auto-quarantined or deleted.
Bottom Line
Effective malware remediation necessitates a structured approach encompassing identification, containment, eradication, and recovery, augmented by post-incident reviews. Integrating advanced machine learning and artificial intelligence technologies bolsters predictive and reactive cybersecurity measures.
Cultivating cybersecurity awareness and adherence to best practices is essential to enhance organizational resilience against malware threats. Continuous monitoring and real-time analysis, alongside a robust cybersecurity framework, are indispensable for early threat detection and compliance with regulatory requirements.
Collaborative efforts, such as sharing threat intelligence and reporting incidents, can also foster a coordinated defense against cyber adversaries. Furthermore, adhering to established frameworks like NIST and CIS Critical Security Controls can guide organizations in adopting a risk-based approach to cybersecurity.
Organizations can enhance their cybersecurity posture and protect their digital assets from malicious attacks by taking a proactive and holistic approach to malware remediation.



Malware Remediation: Best Practices to Safeguard Your Digital Assets (2023)